Note 0018-spam-calls-in-nyc
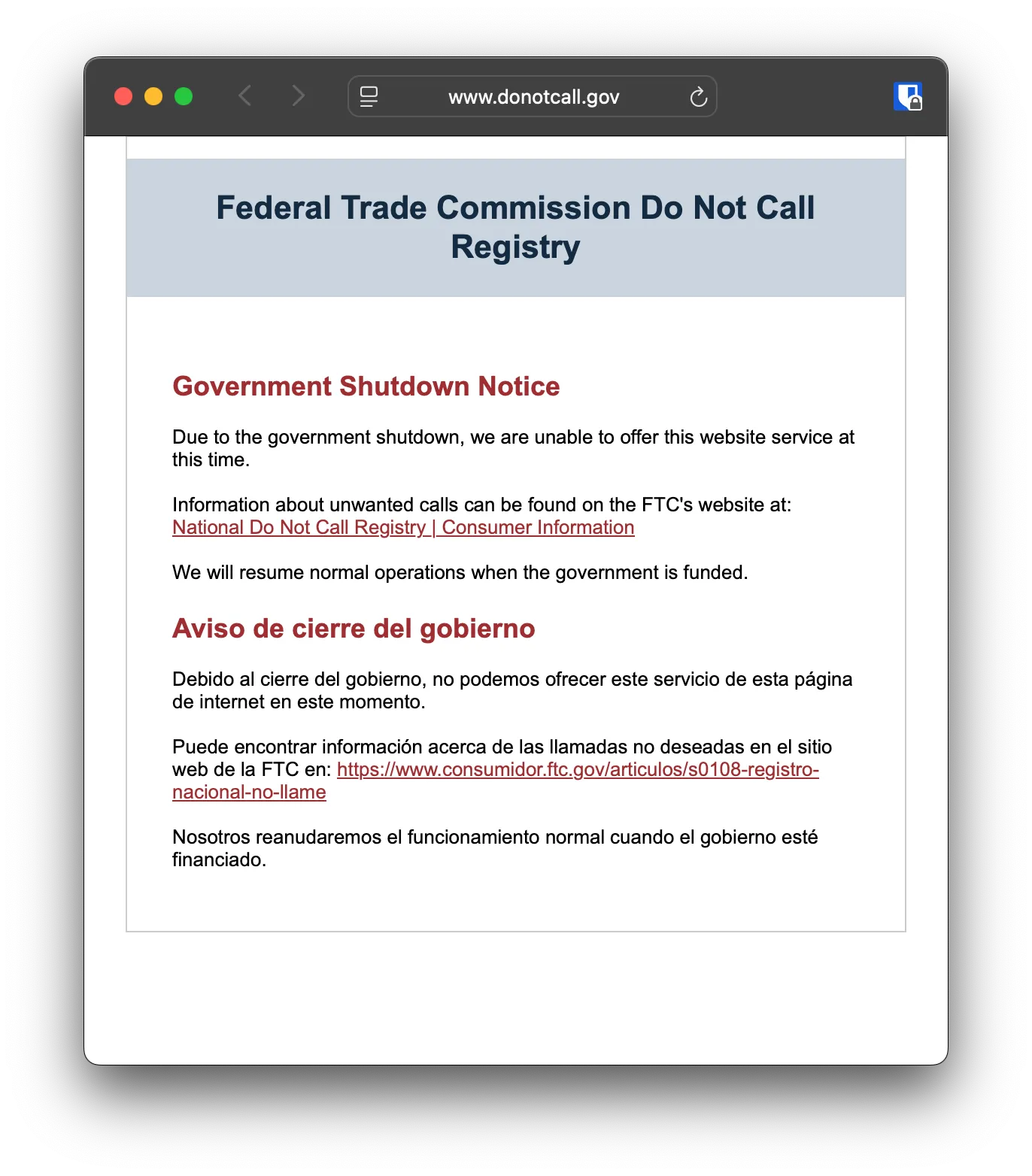
I get around 8-10 calls from 1-8xx numbers every single day, most of them pertaining to financial scams (I get as many text messages as well). A few leave voicemail and the GIF at the end of this note shows about two weeks’ worth. I’ve taken to silencing unknown numbers on my iPhone. The Do Not Call Registry is on a quick little break right now.
Americans have received 4.1 billion robocalls so far this year, or around 135 million each day. A recent survey by Talker Research of 10,500 general population adults indicates that Americans get twice as many scam calls and texts as any other country (and even more than countries that have passed useful consumer protection laws and have functional regulators).
Actually doing something about a problem everyone agrees is awful would be antithetical to Free Market principles, a blot on the idea of Freedom itself, and would precipitate the demise of our thriving republic. Because all regulation is evil, I’ll just sack up and wait for The Market to sort it all out 🥰
A Sample of Laissez-Faire Blessings, Delivered Daily